Is your website WordPress based? It may be in danger.
What are the real risks for websites running on an outdated version of WordPress? Why install updates if the website is working properly? What to do to be able to rest easy?

Photo by: Sébastien Launay
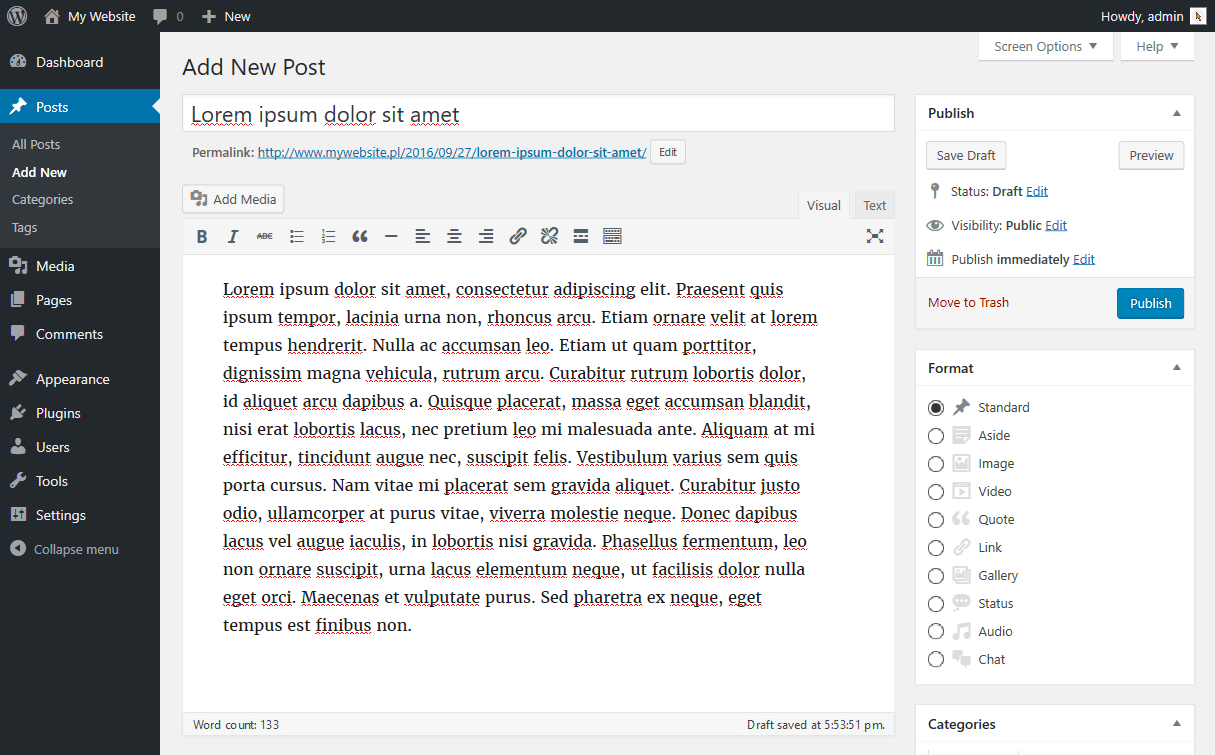
WordPress
WordPress is the most popular CMS in the world. It is being used by most of websites globally (51% to 68%, depending on the source). Its exceptional popularity is due to many factors, the most important of them are:
- Open Source (i.e. open and free code, anyone can edit it)
- truly user-friendly interface – i.e. intuitiveness and ease of use
- short implementation time for a website with standard functionalities
- unique community which eventually gathered around the brand
- huge number of addons (both free and premium) – themes and plugins.
Risks
Unfortunately, the huge popularity of WordPress is also the result of its one, very big disadvantage. The openness of this CMS’s code is being used not only by thousands of programmers but also… hundreds of hackers. They are constantly looking for “holes” in the platform itself as well as in popular plugins, themes.
When a hacker detects a “hole”, he prepares an “exploit”, i.e. a method to use the hole in order to break into the website. He then shares the method he developed with other hackers on shady discussion forums.
Next, whole groups of hackers prepare robots that search for vulnerable websites on the Internet and – often automatically – take control of them.
After a successful hack, hackers use hacked websites in various ways:
- to distribute malicious software (malware)
- to display their content (SEO spam, advertising)
- for DDoS attacks (as a node of the so-called “botnet”)
- to send spam.
If the owner doesn’t notice the break-in quickly and doesn’t respond, there are additional consequences in the form of blacklisting the website/server (then instead of a website, the browser displays a warning first) and a drastic decrease in the search engine’s rating of the website.
Repairing the infected website and the removal of the hackers’ code is a difficult and laborious work. As always in such cases – it’s better to prevent than to react.
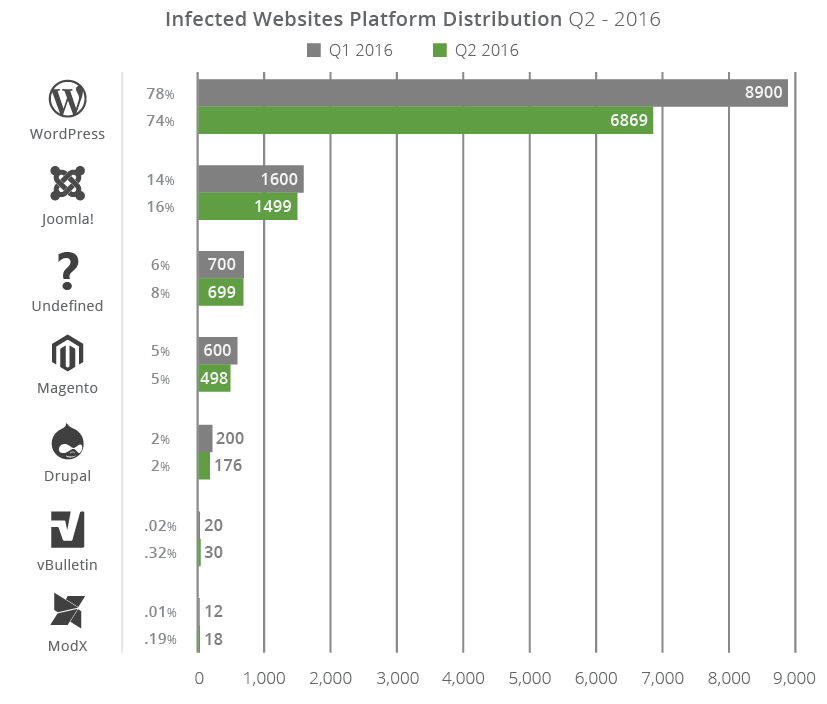
Source: Sucuri Hacked Website Report 2016 – Q2
Prevention
On the other side of the barricade, opposite the hackers, is the army of developers constantly developing WordPress and expanding its ecosystem with new components.
They also read hacking forums and react in the event of new “holes”, quickly preparing a “patch” that eliminates a particular vulnerability.
Such a “patch” is distributed in the form of an update for the platform – and this is why it is very important keep WordPress up to date.
Starting with version 3.7, WordPress gained the ability to update itself automatically. The website administrator simply receives a notification e-mail that a new version has been installed. Unfortunately, automatic updates have several disadvantages:
- they only update the platform, not touching the plugins and themes which can also contain “holes”
- they don’t start at once – meaning that it may take some time from the release of the “patch” to the installation of the update
- they don’t always work correctly.
Regularly updating WordPress and its plugins – apart from security reasons – is also supported by the fact that new versions are simply better than the previous ones, both in terms of functionality and performance.
How to check WordPress version?
If you do not know which version of WordPress is currently running on your website, log into the control panel and immediately after logging in, scroll to the bottom and check the bottom right corner – that’s usually where the number of the version you’re currently running is being displayed.
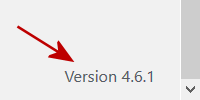
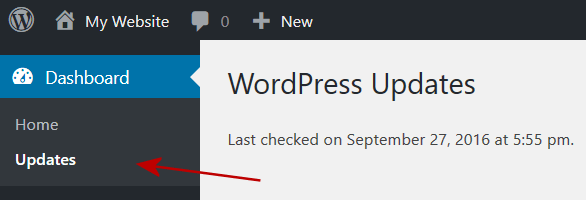
If you can’t see the number in that spot, you’re probably running a version older than 4.1.5. Another place where the version number is being displayed is the “Dashboard > Updates” section.
6.5.2
If you do not have access to the panel – or you’re not even sure whether your website actually runs on WordPress, you can try to check it out remotely using BuiltWith. Enter your website’s address below and click “check”.
Additional features
Regular updates are the basis of WordPress security. But to rest easy you can go one step further and further secure your website.
This operation consists of installing and configuring special plugins, as well as various types of “manual” actions, not only on the website but also on the server.
Here are a few examples of the most commonly used additional security measures:
- changing the standard admin panel log in address and the default admin login
- limiting the number of failed login attempts (block further attempts)
- hiding the version of WordPress you use
- blocking the built-in themes and plugins code editor
- changing the rights to key folders
- changing the standard names of tables in the database.
Summary
WordPress is a very good CMS and with appropriate use, a website based on it can be safe. It is important that it is under the care of someone who knows his subject – who will properly secure it and keep it updated.